|
Information
Management
27
November 2013

The acquisition, distribution,
control and retention of information through the implementation of customary
reporting, record keeping, and protection procedures for privacy and proprietary
information to ensure the necessary business intelligence and institutional
memory is captured and preserved.
After reading this article you
will understand how to
-
acquire the information and
data surrounding and supporting event projects
-
organize information in
ways that ensure efficient retrieval
-
develop distribution
systems that facilitate effective information sharing
-
determine suitable storage
methods for preserving information
-
establish policies and
procedures that protect information from loss or corruption
|
Major Functions |
Performance Elements |
|
Acquisition |
Collect
pertinent data and information
Conduct research and review historical records
Analyze, interpret and evaluate information
Process information in appropriate formats |
|
Organization |
Establish standardized documentation procedures
Organize information according to needs
Develop and implement information retrieval systems
Understand and manage information technology systems |
|
Distribution |
Develop information distribution standards and structure
Create an event production guidebook
Establish data reporting and monitoring systems
Communicate information using various methods |
|
Retention |
Develop record keeping procedures and filing systems
Retain required documents and records
Establish information preservation policies and
procedures
Understand and employ appropriate storage technology
|
|
Control |
Specify methods
to maintain system security and
integrity
Create and implement information access controls
Develop and enforce privacy policies
Comply with intellectual property protection
requirements |
Information is a fundamental
component of planning and producing events. It provides the basis for
initiating, planning, implementing, supervising, and evaluating an event
project. Information is needed for strategy development, decision making,
resource allocation, and problem solving. It is involved in every
administrative, design, marketing, operational, and risk facet of event
management. Information also facilitates collaboration, innovation, enhanced
performance, and continuous improvement.
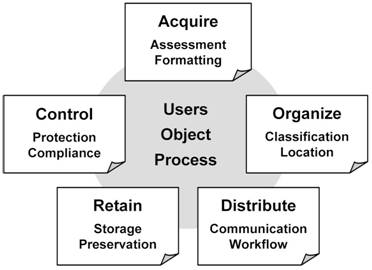
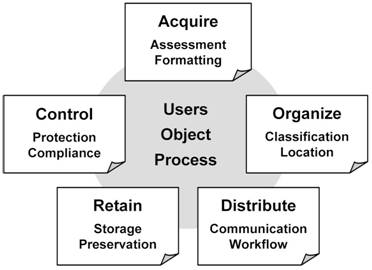
Information management
encompasses the acquisition, organization, distribution, retention, and control
of information throughout the lifecycle of an event project and the endeavors of
an event organization. These activities have specific functions, but are
interrelated and affected by each other and must consider the information users,
objects, and processes when devising the management system. For example, if you
traced a single item of information, such as the event date, throughout its use
for an event project, you would see how it touches every part of the event.
Overview of Information
Management
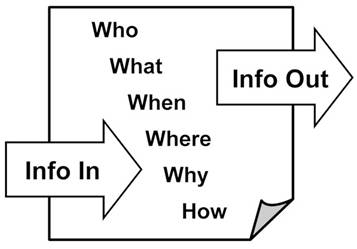
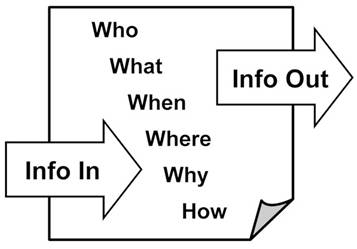
The information management
system must consider who will need the information, what they will use it for,
where they will find it, when they will need it, and why they need it. The
system must also consider the format and value of the pieces of information it
is to accommodate, which can range from physical documents to electronic data
and communications, and public to private or proprietary information. Finally,
the system must consider the processes used to acquire, access, distribute,
retain, and control information, which is based on both its users and the nature
of the objects or items it contains.
Acquisition
From the simplest contact
listing to an analysis of global visitor trends at tourism events, the scope and
nature of information surrounding an event project could be vast depending on
the type of event being produced. Capturing the data you need requires an
understanding of the purpose and uses of the information required, the sources
for where to find it, the methods for acquiring it, and the formats in which it
will be processed.
To give you an example of the
scope of information surrounding a single event project, one meeting planner I
spoke with reported that the on-site documentation needed to manage a recent
four day meeting for 300 people encompassed more than 3,000 pages of
specifications, contracts, transportation schedules, and other documents. The
range of information and documents typically used in planning a conference are
shown below.
Typical documents used in meeting and event planning
|
Accident/incident
reports
Announcements
Articles and by-laws
Attendee brochures
Audience polling
Badges
Banquet event orders (BEO)
Change orders
Charts
Conference handbooks
Conference pack/kits
Confirmations
Coupons
Databases
Directories
E-mails
Evaluations
Event history
Exhibitor manuals
Feedback forms
Floor orders |
Housing reports
Inquiry cards
Invoices
Itineraries
List of attendees
List of participants
Mail and messages
Meeting minutes
Message boards
Newsgroups
Newsletters
On-site registrations
Online registrations
Packing lists
Payment orders
Place cards
Post-convention meeting
(Post-con)
PowerPoint® presentations
Pre-convention briefing
(Pre-con)
Preregistration lists |
Proceedings
Program books
Proposals/bid
quotations
Publications
Questionnaires
Registration kits
Release forms
Reports
Requests for proposal
(RFPs)
Rooming lists
Scripts
Speaker abstracts
Surveys
Tickets
Tour vouchers
Training materials
Transcriptions
Translations
Webinars
Web sites |
You will locate, create, and
receive data throughout the event project. This information is generated through
research, communications, and administrative operations. It must be assessed for
relevancy, accuracy, and urgency. Finally, it must be captured or configured in
suitable formats according to the operational and regulatory requirements of the
event project and event organization.
Collect pertinent data and
information
Information is useless if you
don’t have it. Capture, assemble, and otherwise obtain the information
surrounding and needed for the event project. The first place to start is to
document every decision and everything done in conjunction with an event project
or for the event organization. This documentation provides evidence of actions
taken for current and future use, and should be a standard operating procedure.
Include internal and external
paperwork, physical and digital records, as well as written, electronic, and
verbal communications in your information acquisition activities. Take notes,
summarize, and confirm verbal communications in writing. Review the types of
documents you currently use, such as forms or checklists, and determine if these
are sufficient for your needs. Determine what types of information you could not
remember or had to seek out for your last event project and create a
documentation method that will capture it this time.
Integrate data collection into
the functionality of your various systems. For example, collect full contact
information in online registration or volunteer recruitment systems, which can
then be transferred to a multi-functional database system. Keep in mind,
however, that you are only allowed to collect certain information, and you may
only collect it in acceptable ways. This is particularly true for personal
information and competitive intelligence.
Conduct research and review
historical records
Acquiring the information
necessary for an event project virtually always requires conducting research and
reviewing the records of previous events. There is no reason to reinvent the
proverbial wheel; however there is every reason to improve its design. This is
particularly important in the initiation phase of an event project, but research
and records review is typically necessary throughout the rest of the event
project lifecycle as well.
Research, simply put, is
seeking out information. You might be looking for current marketing trends,
electronic registration capabilities, economic impact data, best practices in
managing risk, or supplier sources for the goods and services you plan to
procure. The more reputable the sources of this information, the more likely the
information will serve your conclusions and decision making well.
The historical records of your
previous events, and reviews or observations of comparable events, contain vast
amounts of practical data and lessons learned. Just like avoiding reinventing
the proverbial wheel, there is no reason to repeat mistakes (vow to only make
new mistakes). Everything from timelines to site plans, committee reports to
publicity campaigns, and every other piece of documentation has a story to tell
if you know how to read it.
Analyze, interpret, and
evaluate information
The information you acquire
must be analyzed, interpreted, and evaluated regarding its relevance and
accuracy. This assessment ensures you understand the information, can integrate
it into your systems according to needs, and can rely on it to meet your needs.
Similarities, anomalies, and gaps can reveal strengths, weaknesses,
opportunities, and threats.
Consider, for example, the list
of sponsors for your previous event. Is the list complete and are the contact
names and numbers current? Are there duplications in the types of sponsoring
companies? Are there potential sponsorship opportunities for companies allied
with current sponsors? Are there sponsors that would likely increase (or cancel)
their investment in the event? Are there sponsorship packages that were not
sold? Which event project teams need to know this information? Answers to these
questions (and more) help direct your sponsorship program activities for the
current event.
Process information in
appropriate formats
Information is received or
acquired in verbal, written, and digital formats, which might or might not be
the format in which it should remain. Most information needs to be converted to
a written format, either as a physical or electronic document (or both) for
distribution, retrieval, and protection. However some types of verbal or visual
information might need to be recorded for evidentiary or programming reasons,
such as before and after walk-through videos of an event site with its owner or
a webinar that will be offered as an on-demand product.
You need to know the purpose
and uses of a certain piece of information to determine the suitable format(s)
it should be kept in. As with any assessment, know the who, what, where, when,
why, and how.
-
Who needs it (and who
should not have access to it)?
-
What will (or could) they
use it for?
-
Where will (or could) they
go to find it?
-
When will they need (or
attempt to get) it?
-
Why do they need (or want)
it?
-
How will they get (or
attempt to get) it?
Operational information
typically needs to be quickly accessible and easily communicated, often in
written form distributed electronically such as via e-mail. Regulatory
requirements typically specify physical documents and precise display and/or
storage procedures. This can include such things as permits, tax records,
insurance certificates, etc.
Organization
As previously noted, there is
an incredible amount of information surrounding an event project. This
information is acquired from many internal and external sources, and required by
many internal and external users to accomplish the goals and objectives of the
event project. An information management system is needed to organize this
information in a manner that takes into consideration the ways in which it is
created, used, stored, and distributed, as well as its accessibility,
availability, and arrangement.
The first component of an
information management system is establishing a standardized documentation
procedure that specifies the purpose and design requirements for documents or
data to be included within the system. This is needed to facilitate the
classification of information according to use and users, and the proper
placement and arrangement of data so it can be accessed as needed.
The structural design of an
information management system (acquisition, organization, distribution,
retention, and control) is fundamentally based on information retrieval – the
ability to locate information when needed, by those who need it. For small event
projects this might consist of a set of folders in a physical or digital filing
cabinet and some event project notebooks. Larger events or event organizations
often use technology systems to manage the data.
Establish standardized
documentation procedures
Documentation is a fundamental
process of event management,
stipulating the need for information throughout the lifecycle of an event
project. Establishing standardized procedures for documentation and document
design provides clear guidance to all system users. It also reduces gaps,
errors, and effort. Once these procedures are devised and users are properly
trained, the functionality of the system achieves its retrievability objectives.
A key component of this
standardization is document design for internally-generated records, which
includes format, content, level of detail, and naming conventions as shown
below. You should develop document templates based on these four features so
that adherence to procedures is easy and consistent. For example, fill-in forms
for incident reports or change orders instantly show users what information is
required.
Design features of a
document management system
|
Format
Nature and purpose of
document |
Type and function of
document
Distribution and
workflow routing
Integration within the
system
Collaboration
functionality |
|
Content
Type of information
|
Collection or
dissemination of information
Author or source of
document
Access rights
(confidentiality) |
|
Level of detail
Scope of information
|
Message or data
Action(s) required
Options, deadlines,
checklists, etc.
Contact information |
|
Naming conventions
Unique document
identifiers |
Title or definition of
document
Date and attribution
Version of document
Repository directory |
Example of document design
features

Organize information according
to needs
The information management
system must organize its contents in a way that allows those who require the
information to find and retrieve it efficiently. Within an event project this
might include categories aligned with the management of the event such as
budget, schedules, procurement, correspondence, and contact lists. However, you
must consider the life of the information to be stored to ensure it will be
accessible to future users; therefore broader categories would likely be
necessary.
Some of the methods used to
identify, organize, and position information include alphabetical, categorical,
chronological, numerical, topical, departmental, and/or project coding.
Typically contact lists are alphabetical, financial records chronological,
staffing plans departmental, and so forth. Supplier lists might be categorical
and/or geographical. Project coding might be chronologically numerical or color
coded categorically by type of event. Determine which methods to be used based
on your needs and users when designing your information retrieval system.
The method(s) chosen to
organize information are incorporated into the document naming conventions,
which are incorporated into your document design strategy discussed above. The
organization method is also factored into the system used in your integration
processes, as well as the distribution, retention, and control aspects of the
information management system and the technology used for it. As you can see,
everything is interrelated and interdependent, but the system usually develops
over time as the event organization matures
Develop and implement
information retrieval systems
Everything surrounding an
information management system is focused on the capability to retrieve
information, and retrieval systems rely on a standardized classification system.
Classification systems provide a way of describing items and ideas, a way of
locating information, and a way of seeing relationships. They provide a
shorthand description of an object within a category and a way to group it with
similar objects or concepts in meaningful clusters using a structure capable of
indicating association by context placement.
For example, how do you locate
a document in your computer, a book in a library, or a web site on the Internet?
In your computer, your documents are usually filed in folders that you have
labeled with short descriptive names; and the computer will not allow you to use
the same name for a document within a folder or a folder within another folder.
In a library, books are numerically coded and you typically find them using the
author’s name or title of the book; and when you locate the book on the shelves
you can see other books with similar topics grouped around it. On the Internet,
you typically type key words into a search engine, which will bring up a list of
web sites that relate to the key words.
For your event, consider the
function each type or piece of information will and could serve. Think about the
various people who will use it, and when, to do their job. How is it acquired
and how many places will it need to go? How is it communicated or distributed
within your event project team and to external stakeholders? Your assessment of
the information acquired will identify the scope and nature of its use and its
integration requirements, which informs the information retrieval system’s
classification design.
As noted before, a single piece
of information can touch every aspect of a current event and future events,
therefore document duplication and/or cross referencing might be needed to
accommodate the various usage attributes. This is accomplished easily within a
computerized system, but will still require a standardized classification system
including an index or directory so that those searching for a document or data
can narrow their search to the most probable location within the system.
Understand and manage
information technology systems
Information technology (IT)
systems are computer- or web-based systems, services, and software applications
designed to acquire, store, sort, compile, communicate, and protect information.
These include such things as databases, networks, word processing programs,
spreadsheet programs, scheduling programs, online registration systems,
transaction processing systems, and countless other tasks and functions
previously done with paper and pencil.
IT systems can automate
administrative tasks, serve as a warehouse for information, create
documentation, generate reports, facilitate data integration, and provide a
platform for internal and external communications. Unless you have a system
designed specifically for your event organization, which is a very expensive
undertaking, there is no single software application that will do all these
things; but you can select applications that can “work” with each other using
similar formats and cross-functionality, such as bundled packages from
Microsoft, Apple, etc.
The hardware and software you
choose and use for your system should be shaped to the workflow process so that
it improves productivity, supports effective decision making, and protects vital
and confidential information. For example, you might invest in housing
management software to arrange hotel accommodations for participants in an
annual national cycling tour. Such software includes
relational database that can automatically
change a sort field item (such as name,
e-mail address, or emergency contact number) throughout the system, and can
automatically generate updates and other communications.
There are thousands of
information management software products, services, and apps (applications) to
choose from, with more developed every day for practically any function you
might want to perform. Avoid purchasing them just because it’s “the latest
thing” and seems to be popular. Make your investment (money and effort)
decisions based on who will be using the system and how, its ability to enhance
productivity, and what will be scalable as your event organization matures.
Distribution
Information is a dynamic asset
of an event project and event organization. It comes in, gets processed into the
information management system, and flows out to those who need it, when they
need it, to accomplish goals and objectives. Similar to money, information is
intellectual capital that is disbursed according to necessity, priority, and
urgency. If the information distribution needs are not clearly defined, valuable
and important data will languish in the system and be worthless.
The facets of the flow of
information
Distribution standards and an
infrastructure must be established so the flow of information is timely and
effective. The capability of this flow increases in importance as the start of
the event nears, and becomes critically important once on site and the event has
begun. The information distribution system must take into consideration the
communication needs associated with the workflow of the event project, some of
which can benefit from technology, but must also include actions to be carried
out by individuals.
Develop information
distribution standards and structure
Information only has value if
it is made available and shared, which occurs formally and informally. This
sharing, or distribution, is enhanced by creating policies and procedures that
standardize formal information sharing and circulation. Generate and integrate
standard operational documents for your event project or event organization into
a distribution network that is configured according to the organizational
structure and workflow of the enterprise.
For example, your event
provides T-shirts for volunteers and your procedures require a purchase order
for purchases above a certain amount. The volunteer coordinator submits a
requisition for the 150 T-shirts; the event manager approves the requisition
because it is in the budget; then the office manager creates a purchase order
and orders the T-shirts. The invoice for the T-shirts arrives with the shipment.
The volunteer coordinator checks the shipment for accuracy and delivers the
invoice to the office manager, who matches it to the purchase order and routes
the invoice to the accounts payable department.
Recognize the value and impact
of information and establish policies regarding distribution, particularly with
regard to internal and external receivers. An internal report on a decision,
action, incident, or acquisition might include information that should not be
communicated outside the organization; however the report might be widely
distributed once private or proprietary data is removed. Determine who needs to
know what information and distribute that information to only those people.
Create an event production
guidebook
The tempo and intensity of
information sharing typically increases significantly as the event approaches,
and becomes crucial during the event. Preparing an event production guidebook,
often called the specifications guidebook or the event bible, ensures you have
the documentation you might need to instruct, verify, and monitor operational
activities just prior to and when on site at the event.
The guidebook typically
includes documents used to check arrangements, confirm agreements, illustrate
compliance, and locate and communicate with staff, vendors, participants, and
other stakeholders. Key documents include contact lists, schedules, contracts,
site or floor plans, significant correspondence, and other pertinent reference
material. Unless required for compliance reasons (such as permits), documents in
the guidebook should be copies, not originals.
The scope, scale, and
complexity of your event project influence the amount of documentation and
information to be included in the event production guidebook. You might not need
the 3,000 pages the meeting planner needed for that four day meeting for 300
people, or you might need a great deal more. Duplicate books or sections of the
master guidebook might be prepared for specific committees or team leaders.
Certain portions of the
guidebook contents might be stored on a digital device such as a laptop
computer, tablet, or smart phone, but digital documentation has its limitations.
There are times when you need a paper document in order to share on-site
information. For example, you would not give your expensive tablet device to
someone to take to a team member on the other side of the event site to confirm
the layout of a stage set-up because that would leave you unable to access
information.
Establish data reporting and
monitoring systems
It is clear that vast amounts
of information surround the production of an event project, even a fairly small
and simple one. In order to increase efficiency and the effective acquisition
and distribution of data, develop reporting and monitoring systems that
automatically generate and circulate information in a timely manner. Such
systems can be procedural and/or technological depending on the protocols and
capabilities of the information management system and the nature of the event
organization.
The features to incorporate
into your reporting and monitoring systems include collecting pertinent data,
scheduling reporting functions, and disseminating information according to
needs. Collecting information regarding the status and effectiveness of planning
decisions allows you to react to performance irregularities and changes before
they become problematic; in other words, change
management. Standard operating procedures are important, but there
will always be surprises.
Your systems should specify the
timing and routing of information, as well as the versioning protocols such as
date, iteration, or status identifiers. These functions are often incorporated
into technological systems so that reports are automatically generated,
electronically routed to appropriate individuals, and instantly stored in the
system’s filing structure. If your system is not technology-based, establish the
procedures for doing all this manually.
Determine which types of
information should be delivered using a push
method (delivered automatically to an individual by the system) or
pull method (acquired from the system by
the individual). For example, a committee report might be sent as an attachment
to an e-mail to all affected stakeholders (push); or an e-mail could be sent
saying the report is available for stakeholders to retrieve if they wish (pull).
Communicate information using
various methods
Sharing information requires
communicating information, which includes verbal, written, aural, visual, and
electronic methods. The methods used are determined based on the nature of the
information to be shared, its intended receivers, the environment in which it is
shared, and the purpose and urgency of the information’s distribution.
Communication often involves a
combination of methods to ensure the intended receiver accurately comprehends
the nature and content of the information. Use written materials in conjunction
with oral communication, and vice versa, particularly for confirmation of
receipt and/or understanding. Use graphics or pictorial visuals to reinforce
written instructions or verbal presentations. Use gestural visuals, such as hand
signals, or aural signals, such as whistles, when verbal or written
communication is not feasible or sufficient.
Information sharing takes on a
more dynamic and urgent character once on site during an event. Noisy
environments, changing conditions, time pressures, critical situations, and
physical and emotional stress all converge to make communication not only more
imperative but more difficult as well. This is when your communication skills
will be tested; make certain you are prepared.
Retention
The information acquired and
generated by the event project or event organization will only be able to serve
current and future goals and objectives if it is preserved and stored.
Information retention is the facet of the information system that captures and
maintains this intellectual capital in a way that archives data objects and
records according to the needs of the users, the object’s format, and the
lifespan of the information.
The design of the retention or
storage system is directly related to the organization and retrieval systems
discussed previously. Record keeping procedures and filing systems must be
developed, and methods for efficiently gathering, keeping, and disposing of
documentation must be devised. Storage methods and technologies are based on the
type of data and its physical medium, which can range from paper or electronic
documents to physical or digital photographs and recordings.
Determine record keeping
procedures and filing systems
Record keeping procedures and
filing systems ensure your ability capture the data and documentation needed for
the current event project, and that these records can be found when needed. The
main objectives for record keeping and filing include consistency, completeness,
and coherency. If any one of these three objectives is not met, achieving the
purpose of retaining records is severely limited.
Establish record keeping
procedures that encompass the types and nature of the records to be kept, who is
to be responsible for creating them or entering the data, when they are to be
generated, and where they are to be stored. Make certain those responsible for
these tasks are given sufficient training so they can perform these functions
accurately. Facilitate consistency, completeness, and coherency through document
design and process standardization.
Implement paper and electronic
filing systems that are organized in a way that will make sense to the user and
be easy to use. Create protocols and procedures for the classification of
records and data, the insertion of records, the access to and removal of files,
the updating of files, and the backup of electronic files. Make certain you have
a way to audit the use and location of records, and monitor this usage so you
can make improvements as appropriate.
Retain required documents and
records
Although almost all the records
and data generated by an event project or event organization have value and
should be retained, there are some documents and records that must be retained
due to legal, regulatory, or fiscal requirements. Depending on the jurisdiction
and the type of event organization, these might include financial, employment,
membership, insurance, and other records, as well as contracts, agreements,
compliance, ownership, and other business documents.
Also consider your operational
requirements for records retention. These records might include budgets,
volunteer records, schedules, site plans, purchase orders, attendee lists, and
other documents. Determine the format requirements for documents and records to
be retained. Some documents must be originals; others may be physical or
computerized copies. Consult with your legal and financial advisors to determine
your document retention responsibilities.
Establish information
preservation policies and procedures
As noted, there are often vast
amounts of information surrounding an event project, and much of this
information is or can be valuable to the future endeavors of the event
organization. You should devise policies and procedures that give structure to
your storage system and protocols for preservation formats, number of copies,
and distribution within the storage system, including where records are to be
stored, for how long, and how they will be disposed of (deleted, transferred to
a historical archive, or destroyed).
First and foremost, ensure
computerized records are backed-up on a regular (and frequent) basis. For
example, saving work product documents on a USB flash drive (also known as a
memory stick or thumb drive) when finished with that document and running a full
back-up at the close of each day is a useful protocol. It is also advisable to
keep a copy of the computer back-up in a separate location.
Many legal or regulatory
documents must be preserved as originals, but you can also scan these and other
event materials so you have a digitized copy to include in your back-up
procedures. Additional preservation policies and procedures might include, among
others, the following.
-
Save all e-mails in
event-specific file folders in your documents system as well as within your
e-mail system.
-
Delete all credit card
numbers and other private data from registration databases once the event is
over (and transactions are complete).
-
Determine the archival and
disposal hierarchy for documents and other materials (schedule, location,
and method).
-
Scan event photographs and
marketing materials.
-
Order and save sufficient
duplicates or copies of all marketing materials, posters, and souvenir
merchandise for future marketing strategy development and sponsorship
solicitation.
-
Delete outdated records as
appropriate (e.g. Date/version, client, supplier, volunteer, sponsor).
-
Destroy paper documents
(including badges, charts, manifests, etc.) By shredding them instead of
discarding them.
-
Maintain an inventory of
records disposed of.
Understand and employ
appropriate storage technology
Storage technology can range
from cardboard boxes to filing cabinets to computers to web-based storage
services. You must consider the type of data and the media in which it is (or
will be) formatted when determining the levels of technology suitable for your
storage systems. As with all facets of the information system, storage methods
must facilitate information retrieval.
With any storage technology
used, items within it must be segregated appropriately and clearly identified
and labeled so it can be recognized “at-a-glance.” Paper or electronic
documents, including paper-to-electronic materials (such as scanned
photographs), should have a document name that indicates its purpose and
event-specific relevance. Event notebooks, file folders, and cabinets should
have event, date, or the range of contents listed. Physical materials such as
marketing materials or merchandise should have a date on or attached to them.
Photographs, negatives, videotapes, CDs, and DVDs should have event and date
labels on the item and the spine of its container.
Large items such as posters or
site plans require special storage containers such as print or map cabinets for
flat storage or tubes for rolled-up storage, although you might also consider
having them scanned as well for an electronic back-up. Please note that
photographs or videos used or distributed outside the event office should always
be copies, and not your only copy, because others do not have a vested interest
in protecting them (I learned this the hard way).
When using web-based storage
services, make certain you understand the capabilities and protocols regarding
access and back-up integrity. These services often offer automatic back-up
service, storage on a web server, file sharing, and numerous other features.
However these services might experience a server crash, be compromised by
malicious software or hackers, or simply go out of business (without warning).
Do not rely on them exclusively for your important files and data.
Control
It is clear that information
has operational and commercial value, which must be protected from accidental or
intentional loss, alteration, theft, or unauthorized access. For some types of
information, such protection is mandated by law and you must comply with
specific requirements. For other types of information, controls are necessary to
ensure your capability to produce the event project.
When you are assessing the
needs (who, what, when, where, why, and how) of the information management
system, you must consider both the uses and potential abuses associated with the
acquisition, organization, distribution, and retention of data. This becomes
increasingly important with the prevalence of IT systems usage. Although
deliberate harm is possible, most problems are caused by accident rather than
intent. Therefore you must consider the system’s weaknesses and develop barriers
and protocols accordingly.
You need to develop
administrative procedures regarding data handling practices and electronic
policies regarding system access, e-mail, permitted and prohibited Internet use,
content and communication restrictions, downloads, confidential and proprietary
information, etc. Give system users sufficient training so accidents are
minimized, enforce policies rigorously, and do not tolerate abuses.
Specify methods to maintain
system security and integrity
There are two facets to
consider when developing policies and procedures to control information within
your information management system: security methods to prevent unauthorized
access and methods for protecting the integrity of the documents and data within
it. Determine the possible barriers for preventing access or alteration and
implement them according to priority and level of vulnerability. These barriers
can include anything ranging from lockable file cabinets to a
rights management component in your IT
system allowing only certain people access to certain documents.
You might use document design
features such as security level designations (“sensitive” or “classified”) to
limit access on a “need to know” basis. Format restrictions such as read-only or
PDF documents might be employed so a document is not easily altered. Delivery
method policies such as e-mail protocols or physical delivery requirements could
be implemented to limit unauthorized distribution problems.
In addition, carefully consider
policies that restrict storage on portable or personal electronic devices, such
as laptops, tablets, USB drives, and smart phones, for on-site and telecommuting
workers. Once documents or data “leave the premises” (are exported from your
main system), you have lost control over them. This will be a significant hazard
if the data is mission critical, proprietary, or governed by privacy
regulations.
Create and implement
information access controls
Although the efficient sharing
of information is an objective of your information management system, not
everyone needs or gets access to everything. Specify the restrictions and
prohibitions regarding who is allowed access to what information and when. Some
access controls might be contractually or legislatively mandated while others
are simply good business practice.
-
Ensure access to computers
and web-based storage sites is password protected, and change the passwords
on a periodic basis.
-
Require users to sign in
with a name and date in a logbook or sheet when removing and returning
documents or items in a physical storage system.
-
Keep personnel and
confidential records in a separated location in physical and electronic
systems, both in the office and when on-site at an event.
-
Use lockable offices,
desks, and file cabinets and institute a key issuance procedure; change
locks as appropriate (if, for example, someone has left the organization
under controversial circumstances).
-
Prohibit distributing
certain documents or information via e-mail (because you can not control its
further distribution).
-
Make certain your IT system
has a designated administrator responsible for assigning access rights.
Of course, the level of access
control measures needed is based on the size, nature, and complexity of the
event project, the event organization, and the information system’s contents.
You need not be obsessed about this; nor should you be complacent regarding the
potential for accidental and intentional abuses. Base the costs (money and
effort) of acquiring and implementing access controls on the financial,
operational, and legal costs of losing the information.
Develop and enforce privacy
policies
There are certain types of
information that are legally and morally considered personal and private, and,
as such, must be protected if collected. These types of information include
identity factors such as name, date of birth, contact information (address,
phone number, e-mail address), social security numbers, and credit card numbers;
as well as personal information such as familial or relationship data, political
or religious affiliation, financial condition, and, in particular, medical
information.
Event organizations often
collect certain types of information in order to conduct employment, membership,
registration, sales, and other activities. The information collected will
primarily be the identify factors needed to conduct a financial transaction or
join an organization (employment or membership). All personal information listed
above can not be required or sometimes even requested (as in employment
situations); however it might be requested by the organization for certain
purposes, but providing this information must be voluntary.
For example, you might request
“in case of emergency” contact information when registering attendees or
participants at an event. You might also request that attendees advise you of
any food allergies or other medically-related special needs. The individual has
the option to provide this information or not, and the organization is then
responsible for using it for that purpose only. All personal and private
information must be disposed of properly when its stated purpose for collection
has expired.
Privacy policies are critically
important when using electronically-based data collection for consumer
transactions. The consumer must be advised regarding who is collecting the
information, the purpose and uses of the information, and how the information
will be secured from unauthorized use. The event organization must protect that
information from internal or external threats; for example, limiting access to
only certain employees within the organization and using only web-based services
that are PCI DSS-compliant (Payment Card Industry Data Security Standard) for
transactions.
Comply with intellectual
property protection requirements
Intellectual property refers to
tangible and intangible products of the human mind, which typically includes
copyrights, trademarks, service marks, patents, and trade secrets. These “idea”
or “knowledge” products have commercial value to owners that is protected by
law.
Overview of intellectual
property
|
Copyright © |
property rights granted for original literary or artistic
works of authorship that have been fixed in a tangible (or digital)
medium of expression |
|
Trademark TM
Registered Trademark ® |
property rights granted
for a word, phrase, or symbol that identifies and distinguishes the
source of the goods of one party from those of others |
|
Service mark SM
Registered Service mark
® |
property rights granted
for a word, phrase, or symbol that identifies and distinguishes the
source of a service rather than goods |
|
Patent |
property rights granted
for the invention of a machine, process, software, article of
manufacture, or original ornamental design, or the discovery of new
variety of plant |
|
Trade Secret |
a unique formula,
process, system, idea, or secret information that provides a competitive
advantage that can only be protected through using nondisclosure or
confidentiality agreements |
Abuses of intellectual property
include, among others, downloading or uploading copyrighted literary works,
music, photographs, or videos, and/or using them without paying licensing fees;
sharing files or software through peer-to-peer networks; and using creative
treatments or ideas acquired from solicited proposals without compensating the
originator (or sending them to another provider to bid on the project). If you
do not prevent these from occurring, your event organization could be liable for
huge fees and penalties.
Establish and enforce policies
and procedures that clearly specify permitted and prohibited use of internal and
external intellectual property. Prohibit such things as copying or downloading
software programs onto additional computers beyond your licensing agreement;
using logos, symbols, graphics, photographs, video, music, content, or other
copyrighted material copied from Internet or elsewhere; and copying and/or
removing proprietary material for personal use or promotion.
Require and acquire
confidentiality or nondisclosure agreements with those in your workforce and
supply chain (direct and indirect
providers) when giving or receiving information that can be considered
competitive intelligence (trade secrets). You might also need specific social
media policies that address what employees and certain stakeholders must not
communicate on various digital sites or platforms according to nondisclosure
agreements.
Clearly specify ownership
rights of creative work product generated by your paid employees, also know as
work for hire, for which the employer typically retains
the copyrights. Also, specify ownership of intellectual property rights on any
creative or business proposals you might send out as an event producer or
organization. Protect your rights and the rights of others.
Summary
To review, this article
examined the ways in which information and data circulate throughout lifecycle
of an event project and the endeavors of an event organization; from the initial
acquisition of information through to its eventual disposal. An information
management system is devised a way that accommodates the needs of its users,
which depends on the types and nature of the information to be included, and
focuses on retrieval capability.
Information sharing is vital to
the success of an event project, particularly during the implementation phase,
and it is critical during an event. Standard operating procedures are a valuable
tool, but there will always be surprises. Communication skills – writing,
speaking, listening, and presenting – are incredibly important to the success of
your information sharing strategies.
Information touches every facet
of an event project and has competitive and operational value to an event
organization. Its capture, arrangement, distribution, retention, and control
will be facilitated by administrative policies and procedures, some of which are
governed by contractual or regulatory mandates. Know your obligations and
opportunities as well as your needs and vulnerabilities, and continually strive
to improve your information management system and strategies.
Terminology
-
change management: the
tactics and processes used to be prepared for and react to changes in a
considered and reasonable manner
-
IT: acronym used for
information technology
-
pull: information acquired
from a system by the purposeful action by the receiver
-
push: information delivered
automatically by a system without initiation by the receiver
-
relational database: a
database that organizes data based on common attributes or sort fields and
can be grouped or manipulated according to data categories
-
rights management: a
software component of a computerized database that can restrict access to
types of documents or data to only specified users or groups of users
-
sort field: an individual
category of data included in a database
-
supply chain: the direct
providers of a product or service and the providers from whom they procure
their goods and service
Back to EMBOK Matrix
|